CRUD API secured with Microsoft Entra
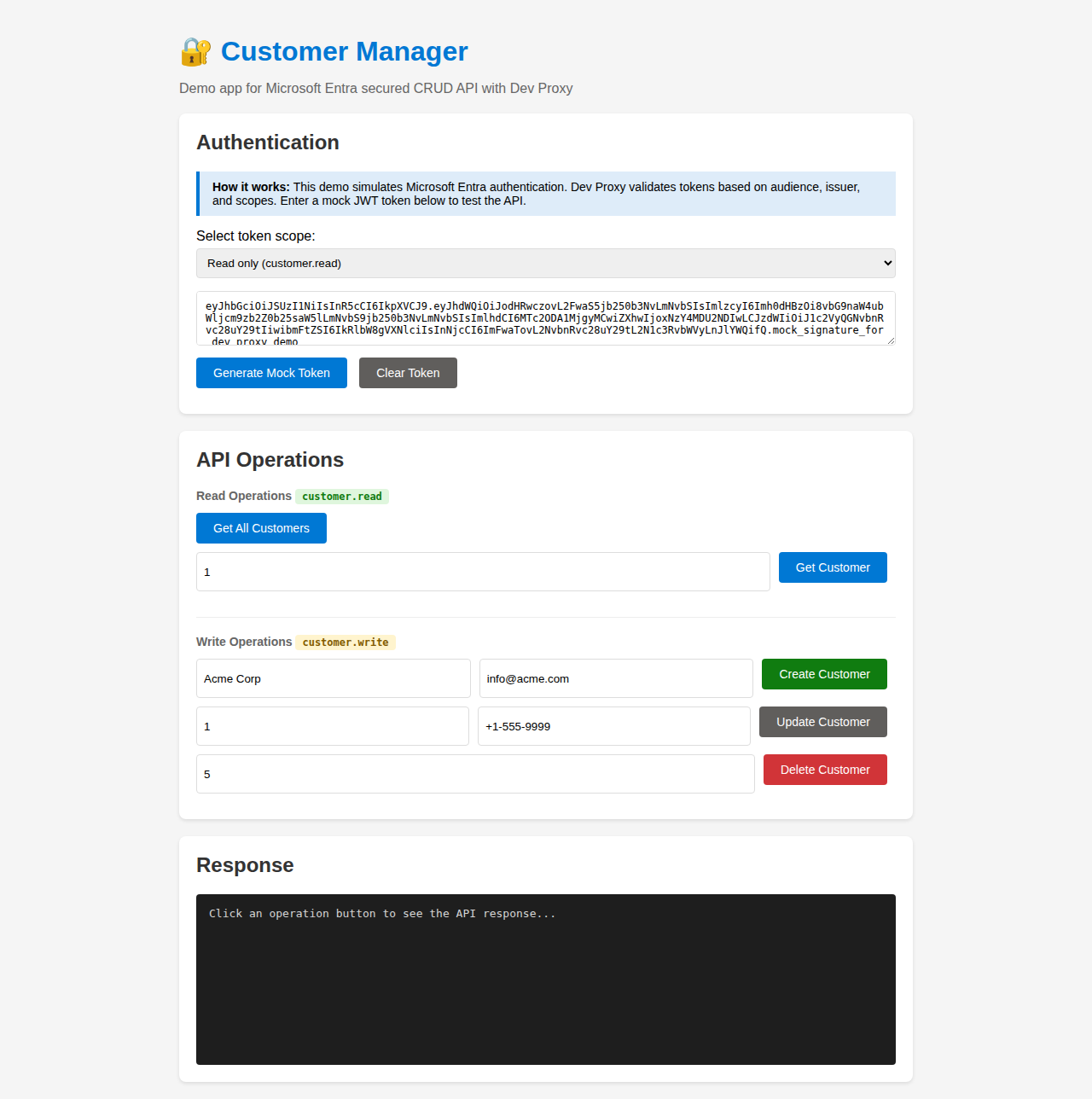
This sample demonstrates how to simulate a CRUD API secured with Microsoft Entra authentication. It includes a demo web application that shows authentication with different scopes and CRUD operations with Bearer token authorization.
CRUD API secured with Microsoft Entra
Summary
This sample demonstrates how to simulate a CRUD API secured with Microsoft Entra authentication using Dev Proxy. It includes a demo web application that shows how to:
- Authenticate with Microsoft Entra using different scopes
- Call CRUD API endpoints with Bearer token authorization
- Handle different permission levels (read vs write operations)
Use this sample to build frontend applications before the backend API exists, with real Microsoft Entra authentication flow.
Compatibility
Contributors
Version history
| Version | Date | Comments |
|---|---|---|
| 1.0 | January 16, 2026 | Initial release |
Prerequisites
- Dev Proxy
- Node.js LTS (for http-server)
Minimal path to awesome
- Get the sample:
-
Download just this sample:
npx gitload-cli https://github.com/pnp/proxy-samples/tree/main/samples/entra-secured-crud-apior
-
Download as a .ZIP file and unzip it, or
-
Clone this repository
-
- Navigate to the sample folder:
cd samples/entra-secured-crud-api - Run
npm installto install dependencies - Run
npm startto start Dev Proxy and the web server - Open http://localhost:3000 in your browser
- Select a token scope (read, write, or both) and click Generate Token
- Click the API operation buttons to see the responses
Features
This sample demonstrates Microsoft Entra secured APIs using the CrudApiPlugin.
API Endpoints
The API is exposed at https://api.contoso.com/v1/customers with the following operations:
| Endpoint | Method | Required Scope | Description |
|---|---|---|---|
/v1/customers | GET | customer.read | Get all customers |
/v1/customers/{id} | GET | customer.read | Get a customer by ID |
/v1/customers | POST | customer.write | Create a new customer |
/v1/customers/{id} | PATCH | customer.write | Update a customer |
/v1/customers/{id} | PUT | customer.write | Replace a customer |
/v1/customers/{id} | DELETE | customer.write | Delete a customer |
Authentication Configuration
The sample uses the following Microsoft Entra configuration:
| Property | Value |
|---|---|
| Audience | https://api.contoso.com |
| Issuer | https://login.microsoftonline.com/contoso.com |
| Read Scope | api://contoso.com/customer.read |
| Write Scope | api://contoso.com/customer.write |
Demo App Features
The included web application demonstrates:
- Token generation - Generate JWT tokens using Dev Proxy’s token API with different scopes
- Scope selection - Choose between read-only, write-only, or both scopes
- CRUD operations - Test all API operations (GET, POST, PATCH, DELETE)
- Response visualization - See full API responses including headers and status codes
Customizing Token Validation
To enable full token validation (for use with real Microsoft Entra tokens), update the .devproxy/customers-api.json file to add validation options:
{
"entraAuthConfig": {
"audience": "https://api.contoso.com",
"issuer": "https://login.microsoftonline.com/YOUR-TENANT-ID/v2.0",
"validateSigningKey": true,
"validateLifetime": true
}
}[!NOTE] Update the
audienceandissuervalues to match your actual Microsoft Entra app registration when testing with real tokens.
Help
We do not support samples, but this community is always willing to help, and we want to improve these samples. We use GitHub to track issues, which makes it easy for community members to volunteer their time and help resolve issues.
You can try looking at issues related to this sample to see if anybody else is having the same issues.
If you encounter any issues using this sample, create a new issue.
Finally, if you have an idea for improvement, make a suggestion.
Disclaimer
THIS CODE IS PROVIDED AS IS WITHOUT WARRANTY OF ANY KIND, EITHER EXPRESS OR IMPLIED, INCLUDING ANY IMPLIED WARRANTIES OF FITNESS FOR A PARTICULAR PURPOSE, MERCHANTABILITY, OR NON-INFRINGEMENT.
